
Recognise App Security Vulnerabilities Beforehand With Application Threat Modeling
Do you want to eliminate every vulnerability and application threat before it cracks open your software security?
Research shows that it’s more intelligent to fix software problems early in the development stage than waiting long into deployment to perform the traditional penetrate and patch model, especially when it involves software security.
According to Statista, over 9 billion data points were revealed during a summer 2018 security breach of Apollo’s sales intelligence company. Imagine the multiplier effect this can cause for other partnering companies. Today, the greatest danger we face is cyber breaches. A host of confidential information could be stolen right from under your nose with you capable of doing absolutely nothing about it. It’s a situation we all dread.
Threat modeling helps to identify and prioritize possible vulnerabilities and threats before the software is built. Threat modeling could apply to a wide range of networks, systems, the internet, applications, and software. Trapping these issues from the bud with an effective application threat modeling approach will sharpen the safety of software you launch.
Why should you do the threat modeling of your application?
The goal of threat modeling is not only to identify vulnerabilities for mitigation but to improve the overall presence of the application security.
This approach can help the software development process in the following way:
- Design secure software
- Develop security test scenarios to examine security requirements
- Highlight and build the required control protocol
- Balance risk, control, and usability
- Identify necessary control development and unnecessary zone base on potential risk
- Record all threats and mitigation approaches
- Prevent compromise of business goals/requirements in the face of threats or malicious actors
- Ensure compliance
- Guide efficient investment of resources; prioritize security and other development responsibility.
- Link security and DevOps by creating a DevSecOps culture.
What is application threat modeling?
Threat modeling, also called Architectural Risk Analysis is a procedure for optimizing Software security by IT professionals by identifying potential security threats and vulnerabilities, quantifying the seriousness of each while prioritizing techniques to mitigate attacks and protect software.
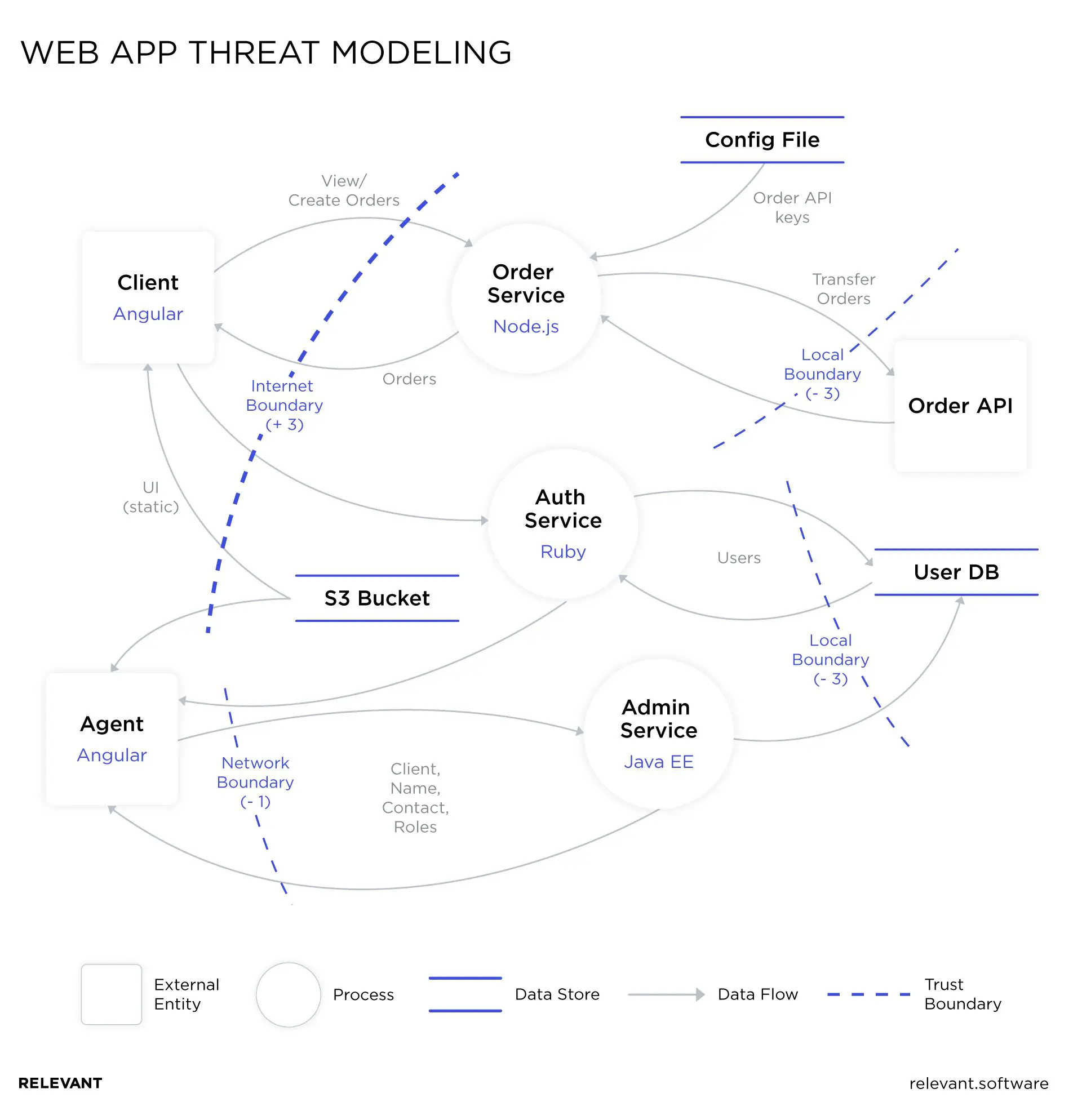
Let us show you how it is done with this image.
Threat modeling methodologies
Here is the thing, not all threat modeling methodologies work the same way if you might be thinking of jumping onto the next one you see advertised on google. However, there are various threat modeling methodologies used for enhancing IT cybersecurity practices with unique results.
Here is a highlight of the strong methodologies applied today:
OCTAVE
OCTAVE which stands for the Operation of critical threats, assets, and vulnerability framework. This methodology serves to identify and manage information security risks. OCTAVE follows a detailed approach that evaluates the organization to identify essential information assets, threat valleys, and vulnerability that may expose the organization to potential risks. By bringing together the information assets, threats, and vulnerabilities, the organization can begin to understand what information is at stake. This approach allows organizations to direct, prioritize, and manage security practices to reduce the overall risk exposure of their information assets.
STRIDE
STRIDE points to 6 important security risk categories which are; Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privileges. STRIDE is one of the most mature threat modeling methods in cybersecurity. Sub-classifications
- Spoofing – is the unauthorized use of identity markers, such as passwords and usernames, to gain unauthorized access to private information. Other examples of spoofing identity are forging email addresses or the modification of header information in a request to gain unauthorized access to a software system or even pretend to be someone other than yourself.
- Tampering – Tampering involves a usurper making modifications to data. Examples of tampering with data include modifying data in a database, changing data as it travels over a network, and modifying data in files or a network.
- Repudiation – Repudiation is the explicit denial of performing actions where proof cannot be ascertained.
- Information Disclosure – Information disclosure threats involve cybercriminals gaining unauthorized access to confidential information. For example, attackers could obtain sensitive system information (server OS version, application framework version, etc.) to further craft a highly specialized attack vector on various platforms.
- Denial of service (DOS) – A denial of service threat involves denying legitimate users’ access to systems or components. They could then be overloaded to a point such that they cannot fulfil legitimate requests.
- Elevation of privilege – An elevation of privilege threat involves a user or a component being able to access data or programs for which they are not authorized for insider threat detection.
PASTA
PASTA stands for the Process for Attack Simulation and Threat Analysis (PASTA) which is a risk-centric threat-modeling framework developed in 2012. It’s a seven-step risk-centric methodology that aligns business objectives with technical requirements to provide organizations asset-centric mitigation strategy.
This method elevates the threat-modeling process to a strategic level by involving key decision-makers, while adopting security inputs from other key departments like governance, architecture, operations and development.
PASTA leverages simulation to provide experts with enough insights to know what an attacker’s perspective is on applications and infrastructure better, and then develop threat management, enumeration, and scoring processes.
Trike
The Trike was created as a security audit framework that uses threat modeling as a technique. The first step to applying Trike is defining a system, then understanding and enumerating system actors, actions, rules, and assets when building the required model.
It looks at threat modeling from a risk-management, and defensive perspective—Trike uses a unique security auditing process from start to finish, including risk management. Trike allows organization stakeholders to create accepted levels of risk for each asset class, thereby enabling security teams to develop threat/requirement models to audit the entire process. Security experts then produce a threat model after analyzing the requirements model.
VAST
The Visual, Agile, and Simple Threat modeling (VAST) methodology was conceived after reviewing the shortcomings and implementation challenges inherent in the other threat modeling methodologies. The founding principle is that to be effective, threat modeling must scale across the infrastructure and entire DevOps portfolio, integrate seamlessly into an Agile environment, and provide actionable, accurate, and consistent outputs for developers, security teams, and senior executives alike.
We can classify Automation, Collaboration, and Integration as the three pillars of scalable threat modeling linked to VAST. VAST focuses on developing two main threat models; operational threat models and application threat models. As a result of an advisory point of view, Operational threat models are created to focus more on the DFDs. Meanwhile, Application threat models use a process-flow diagram, representing the architectural point of view. The VAST methodology is ideal for enterprise businesses seeking actionable threat models unique to the needs of various stakeholders.
Application threat modeling process
Each threat modeling methodology consists of their particular unique steps and techniques that make each different. But basically the goal of a threat model is to answer four questions:
- What are we working on?
- What can go wrong?
- What actions are we taking?
- Did we do a good job?
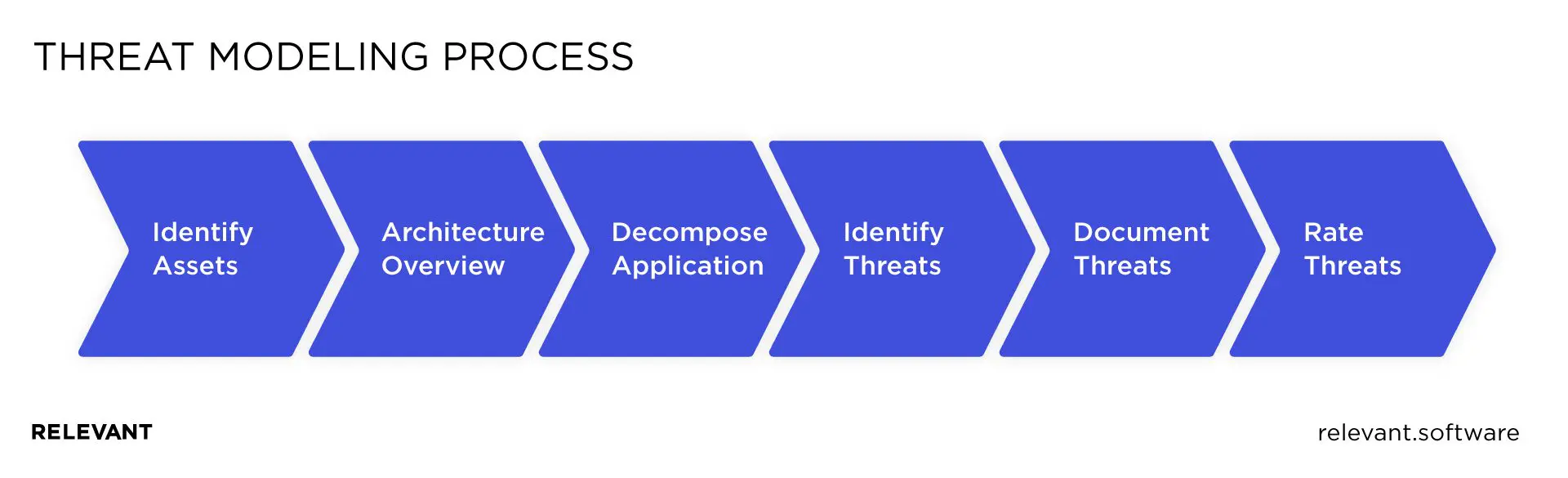
The threat modeling process should, in turn, involve four broad steps, each of which will produce an answer to one of those questions.
- Decompose the application or infrastructure
- Determine the threats
- Determine countermeasures and mitigations
- Rank the threats
We follow these steps while building applications for our clients to ensure their software security.
Summary
Threat modeling is a necessary part of secure software development and the first step to implementing DevSecOps culture. It helps to identify vulnerabilities early on before hackers do.
Our cybersecurity experts will help you not only make the right choice of threat modeling model but also implement it, ensuring the overall security of your application. Contact us now to design a secure application architecture and eliminate vulnerabilities.



